Sublime Text 2 is a text editor for OS X, Linux and Windows, currently in beta.
 Thieves target health insurance policy numbers
Thieves target health insurance policy numbers
Victims often don’t realize they’ve been targeted until they discover a drop in their credit score or until a collection agency comes after them for unpaid medical bills, said Jim Quiggle, director of communications for the Coalition Against. Insurance Fraud a group that includes insurers, consumer activists and government officials. While most of the cost of medical identity theft is borne by the health care industry and government, the Poneman Institute estimates that about 36 percent of victims in 2013 incurred out-of-pocket costs such as reimbursements for services provided to impostors, legal fees and identity protection services. The average cost for these victims amounted to $18,660; in a few cases, it exceeded $100,000.
Medical identity theft can happen in several ways. In one common scenario, the criminal persuades a consumer to divulge his health insurance number. Strategies for collecting these numbers can be highly sophisticated, especially when crooks operate in teams, Quiggle said. “They might invite seniors to bogus health fairs where they take their blood pressure and give them some nutritional supplements and ask to see their Medicare cards.”
Jennifer Trussell, who investigates medical identity theft for the Department of Health and Human Services’ Office of Inspector General, has seen cases where criminal rings target senior centers or homeless shelters and offer people $50 for, say, their Medicare number. “That information is sold again and again,” she said.
Even though the victims in these instances voluntarily share their numbers, they may not realize the impact, Quiggle said. “They'll discover to their horror that their Medicare account is being rifled and even maxed out by thieves who are making false claims against their policy.”
Some cases are perpetrated by employees of medical offices or even health care providers. Trussell worked on a case involving an Iowa chiropractor who had lifted the names and dates of birth of more than 200 patients to collect fraudulent Medicaid payments. In another case, a Baltimore pharmacy owner and two employees were indicted for allegedly submitting bogus claims for prescription refills to Medicaid and Medicare.
Sometimes medical identity theft happens with the cooperation of the victim, who allows a family member or acquaintance to use his health insurance card to obtain care. Poneman Institute founder Larry Poneman said these “Robin Hood” crimes made up 30 percent of the medical identity thefts his group studied in 2013.
Giving your insurance number to someone in need might seem like a generous thing to do, but it’s still a crime and you could suffer consequences if the visits rack up bills that go unpaid or result in incorrect additions to your medical records, Poneman said. If an impostor’s blood type or medical condition gets added to your record, you could end up receiving inappropriate or even life-threatening treatment.
Electronic medical records make your medical data easier to steal, because any clerk with access to patient records can load patient information onto a thumb drive and sell it to cronies or crime rings, Quiggle said. And because the Internet makes electronic records easy to share, tracking down all the providers who have received incorrect data can be difficult.
So how do you protect yourself? Never give your medical identity credentials to anyone but those with a legitimate reason for needing this information, such as the billing person at your doctor’s office, Quiggle said. Treat with suspicion anyone who asks you for your insurance number without a good reason, and never give these numbers to telemarketers or callers conducting “health surveys.”
Closely scrutinize the “Explanation of Benefits” or “Medicare Summary Notice” documents that are sent to you to make sure that you actually received the services and products listed, he said.
If you see anything suspicious, ask to see your medical record to look for mistakes or evidence that your identity has been compromised. “A lot of people don’t realize that they have the right to read their medical records,” Poneman said. He recalls a case where a woman who stood more than 6 feet tall went in for bypass surgery; her medical record, however, showed that she was just over 5 feet tall because, unbeknown to her, an impostor had used her identity to receive care. Had she been given anesthesia and other drugs based on the impostor’s size, she could have faced serious problems with the surgery.
Think twice before sharing detailed medical information on social media, Trussell said. Posting a medical diagnosis on social media is akin to posting your address along with the dates that you’ll be away on vacation. An impostor could use that information to obtain services that might not raise red flags with your insurer. For instance, if you tweet about your diabetes diagnosis, Trussell said, it’s possible that “next thing you know, you’re getting diabetes test strips you didn’t order or receive billed to your insurance company.”
If you discover that your medical identity has been stolen, your first step should be a call to the police, Ponemon said. Next, call the Federal Trade Commission’s identity theft hotline, 877-ID-THEFT, or report the problem online at www.ftc.gov/idtheft. Report Medicare- or Medicaid-related crimes to oig.hhs.gov/fraud/hotline or by calling 800-HHS-TIPS.
10 Tips: Stay in Shape While Traveling
Even though you’re out walking all day, and it may seem like you’re getting a lot of exercise, you’re probably also eating a lot of high-calorie and fatty foods that pretty much negate all the good you’re doing with the walking, hiking and stair-climbing.
Those extra pieces of cake and pie for dessert aren’t helping either. Contrary to popular belief, calories do count on vacation, as much as you wish they didn’t. So, if you want to stay on track and earn those meals, you might want to add additional exercise to your vacation itinerary:
Get outside
I love to be outdoors when I travel. It’s the best way to see your destination, so why not get out a little more and burn extra calories?
- Go running – You’re going to bring along a pair of walking shoes anyway, so why not make them running shoes that are also good for walking. If you run at home, then keep your routine set and get up early to run around the block or the hotel grounds.
- Jump rope – This is an easily packable item and gets you great exercise anywhere you have some extra room. Not just little kids love to jump rope. It’s fun and helps you tone and keep in shape. Make sure you buy a nicely weighted one that will stand up to the rigors of the road
You walked all day yesterday, but you got up early in order to watch the news or eat breakfast in your room. As much as you know you should put on your workout clothes and hit the gym, the thought of looking presentable just doesn’t sound appealing. You aren’t alone. While you’re waiting for your bagel to toast or you’re listening to the weather report, you can take advantage of the floor space in your room to get in a quick workout.
- Chair crunches – If you have a chair, you have a low-impact gym. Work your abs by sitting on the edge and pull your legs up or pump your legs as if you are riding a bicycle.
- Do lunges – You’ll feel a lot less awkward doing them in the privacy of your room than out in public, too.
- Calf raises – Do these anywhere, like while you are brushing your teeth, making oatmeal or waiting in line to get into the Louvre (for bonus exercise points).
Your hotel or rental property might have some useful ways to help you work out. If the weather cooperates enough to be outside, then you’re in luck.
- Go for a swim – Almost all hotels have a pool. Pack your swimsuit and you can get in some laps. If a fancy indoor pool is available, then you can swim if the weather is uncooperative.
- Use the stairs – Walk or run up the stairs to your room and you’ll start to feel the burn. Generally, the stairwell is pretty private, so you also won’t be disturbing others if you are up early or late doing this.
- Go for a run – Not close to a park or afraid to go out running in unfamiliar terrain? Strap on your running shoes and do laps around the hotel. Chances are it is surrounded by a parking lot and/or sidewalks that make it easy to get your strides in.
 Gold Starts New Week On Upbeat Note
Gold Starts New Week On Upbeat Note
Investing.com - Coming off the best weekly performance in a month last week, gold futures again traded higher in the early part of Monday’s Asian as traders continued to boost the yellow metal higher.
On the Comex division of the New York Mercantile Exchange, gold futures for September delivery rose 0.43% to USD1,377.10 per troy ounce in Asian trading Monday. The September contract settled up 0.74% at USD1,371.20 per ounce last Friday.
Gold prices added 4.55% on the week, the strongest gain since the week ending July 12. The precious metal has rebounded 16% since hitting a 34-month low of USD1,180.15 a troy ounce on June 28.
Gold futures were likely to find support at USD1,304.50 a troy ounce, the low from August 9 and near-term resistance at USD1,391.35, the high from June 17.
Gold was embraced as a safe-haven play last week amid some concerning U.S. data points that weighed on stocks. In U.S. economic news out last Friday, the Thomson Reuters/University of Michigan's preliminary reading on the overall index on consumer sentiment for August fell to 80 from 85.1 in July. The August reading was the worst in four months.
The Commerce Department said housing starts rose 5.9% to 896,000 units. Economists expected housing starts to rise to 900,000 units.
Data indicate traders are boosting their long bets on bullion. According to the U.S. Commodities Futures Trading Commission, net long positions in gold futures and options contracts jumped 18% to 56,604 contracts for the week ending August 13.
Demand in India and possible mine strikes in South Africa may boost prices in the next four to five weeks before an industry conference in Denver, Bloomberg reported, citing a JPMorgan research report published last week.
Elsewhere, Comex silver for September delivery inched down 0.06% to USD23.307 per ounce while copper for September delivery rose 0.30% to USD3.372 per ounce.
RELATED ISSUE:
http://www.bookrix.com/search;keywords:%20%20tana%20goldfields,searchoption:books.html
 Printing with all the connecting lines.
Printing with all the connecting lines.
Greetings,
I am teaching robotc coding. Your program showing all the logical connections (do/while, if then else, while, etc) is wonderful for helping students (and the teacher) see the relationships between the parts of the code. I would love to be able to print the code with all the colors and the connecting lines so I can insert it into a document for each exercise. For long code (over 60 lines or so), it would help to be able to insert a page break.
Thanks,
Blaine

 Massage center in denver | Spa and wellness center in denver
Massage center in denver | Spa and wellness center in denver
Bedpage is a website through which you can find the best spa center in denver and massage center in denver.
I recommend bedpage for everyone who wants to go spa in nearby location. Bedpage gives you best results than other sites regarding to spa and massage centers.

 Post Post Crisis Era to Continue
Post Post Crisis Era to Continue
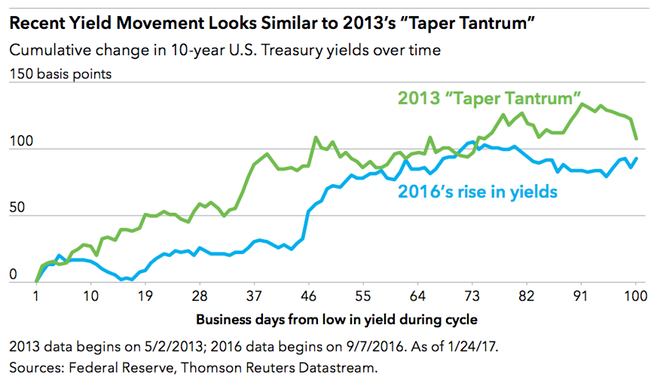
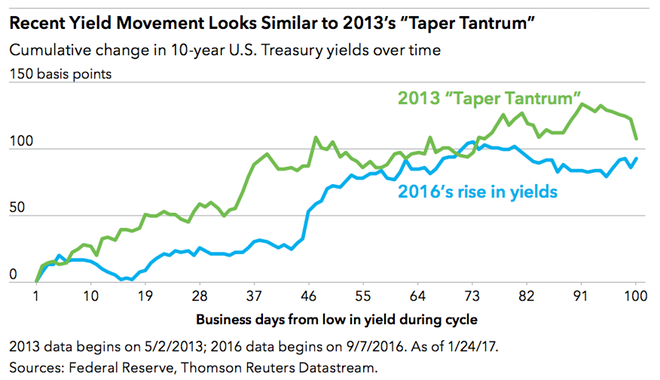
We’ve talked about the post-post-crisis era as one that is neither risk-off (a period like the financial crisis, when investors shun riskier assets) nor risk-on (a period like the post-crisis period, which we define from March 2009 through November 2014, when investors embrace riskier assets). In a post-post-crisis landscape, markets have a mixed outlook, in which growth is uneven and interest rates remain low.

 Post Post Crisis Era to Continue
Post Post Crisis Era to Continue
We’ve talked about the post-post-crisis era as one that is neither risk-off (a period like the financial crisis, when investors shun riskier assets) nor risk-on (a period like the post-crisis period, which we define from March 2009 through November 2014, when investors embrace riskier assets). In a post-post-crisis landscape, markets have a mixed outlook, in which growth is uneven and interest rates remain low.

 Five Keys to Investing in 2017
Five Keys to Investing in 2017
#1: Uncertainty Is a Sure Thing. Keep Calm and Carry On.
There are nearly 50 million people over 65 in the United States, and many of them have one thing in common: They want their dividends. Millions of retiring baby boomers need income, but they may have to search far and wide for yield.
Don’t get too high or too low. Try to maintain an even keel. Fight fear with facts.

 Online Info Blog: Avoid scams
Online Info Blog: Avoid scams
The web can be a great place, but not everyone online has good intentions. Here are three simple ways to avoid scammers and stay safe on the web:
Customer support service by UserEcho